Unlock the potential of data securely using privacy-enhancing technologies
By combining and enriching data, we can create new insights and innovative solutions. We’ll be able to make healthcare more personal and accelerate the energy transition, for example. But how do you handle sensitive personal data securely? At TNO, we’re working on privacy-enhancing technologies, such as multi-party computation (MPC), federated learning, and synthetic data generation. Discover how you can use these to create value as an organisation, while also respecting privacy.
Hospitals that can provide personalised care, based on your specific situation. Medical specialists who can gain an even more reliable understanding of how diseases such as cancer and cardiac insufficiency progress. Law enforcement authorities and financial institutions that combine their data, greatly enhancing their effectiveness in the fight against fraud and money laundering.
Exchanging data has huge potential for the economy and society. Recent research has shown that our GDP could actually rise by 1.5% if organisations seized the opportunities offered by data sharing (source: OECD). But how do you do that effectively and – above all – securely?
Discover privacy-enhancing technologies
Privacy-enhancing technologies (PET) offer solutions. Together, these technologies enable organisations to conduct joint data analyses in a privacy-friendly manner.
Federated learning, for example, brings the machine learning model to the data, rather than the other way round, so that you don’t require a central database. And secure multi-party computation uses a ‘toolkit’ of cryptographic techniques that enable multiple parties to use data jointly for making calculations, as if they had a shared database.
With the help of synthetic data, you can analyse and use data without violating the privacy of individuals, while still retaining the information from the original data. We’ve set out all these technologies and their applications in our white paper, ‘Finally, a privacy-friendly way to use data’.
Zero-Knowledge Proofs
Zero-Knowledge Proofs (ZKPs) are cryptographic techniques that allow someone to prove that a statement is true without revealing the underlying data. This offers a solution to the tension between privacy and functionality, for example in age verification on social media or when applying for a mortgage. Read all about it in our whitepaper Private Evidence (pdf).
From data sharing versus privacy, to creating value with privacy-friendly data analysis.
How can TNO help your organisation?
At TNO, we assist in selecting the right privacy-enhancing technologies that contribute to privacy-friendly data collaboration. We conduct joint research into the requirements and wishes of your organisation and recommend the most effective solution that enables secure data exchange. We bring together the parties needed to address a societal problem. We also collaborate with market parties that can implement the technological solution in the operational setting of your organisation. Tools you can also use yourself include:
PET Brochure
Would you like more insight into the different types of PETs? Then download this brochure from the AIVD (Dutch). The characteristics of various PETs, including their application domains and a concise explanation of how they work, have been provided by TNO for this brochure. For illustration purposes, PETs are compared on key aspects such as security guarantees, maturity, and scalability.
PET decision framework
Setting up new collaborations and using new technology offers opportunities but also requires an investment of resources. The PET decision framework (NL) (pdf) helps public managers in 5 steps to assess whether it is worthwhile to invest time and money in exploring the use of PETs in new collaborations.
PET explorer with decision tree
Once the decision has been made to use PETs, TNO offers a tool for specialists to explore the available technological options. This online tool helps you gain a better understanding of your specific challenge and guides you to an appropriate PET solution. This includes the use of an interactive decision tree.
PET Lab
Would you like to learn more about open-source PET building blocks and complete solutions? Read more about TNO’s PET Lab.
Secure Multi-Party Computation
How can you work on information securely together with others, without revealing underlying sensitive data?
Federated learning
How can you analyse large amounts of data, without violating individuals’ right to privacy?
Synthetic Data Generation
How can you learn from personal data without violating privacy?
Get inpired
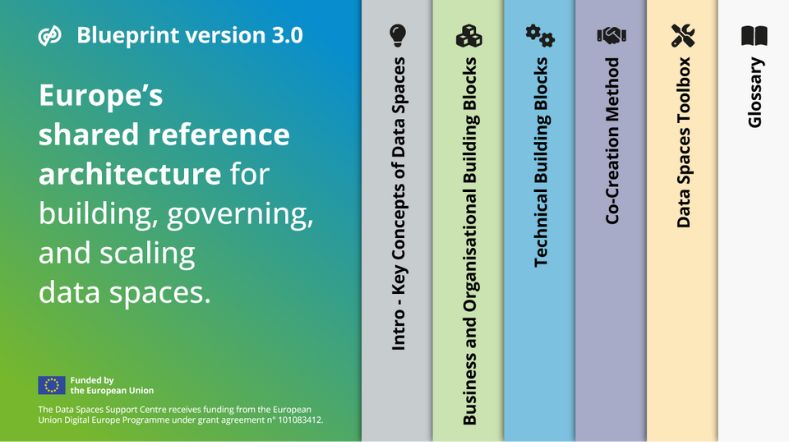
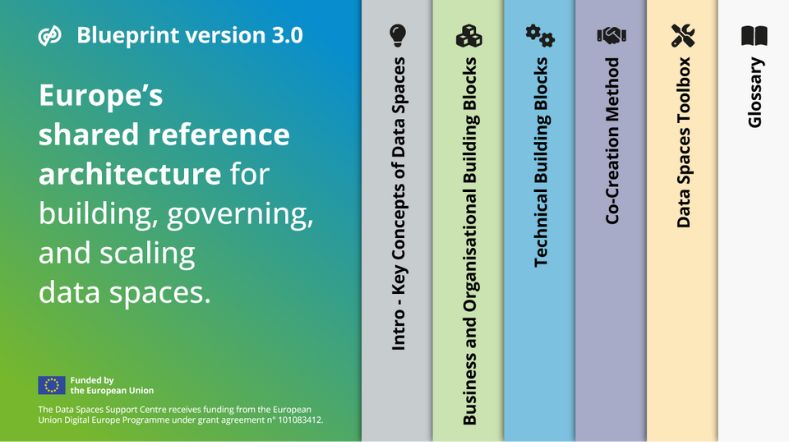
New blueprint helps organisations share data reliably
Working towards better risk prediction for cardiac patients through secure data collaboration


Assuring Digital Identity


Rules as Code


Digitalisation and sustainability: how AI can help



