
SSI Lab
The TNO SSI Lab is a cross-project initiative that develops and validates technologies and standards for self-sovereign identity (SSI). Businesses can use this very easily for negotiation and execution of (business) transactions with other organizations and individuals alike.
The lab develops open-source tooling for SSI-wallet interoperability TNO EASSI, as well as open-source terminology tooling
The purpose of the lab is to provide tooling and hands-on knowledge for governmental and business projects that aim to implement SSI technology to further rationalise and automate and rationalise decision processes.
What is SSI?
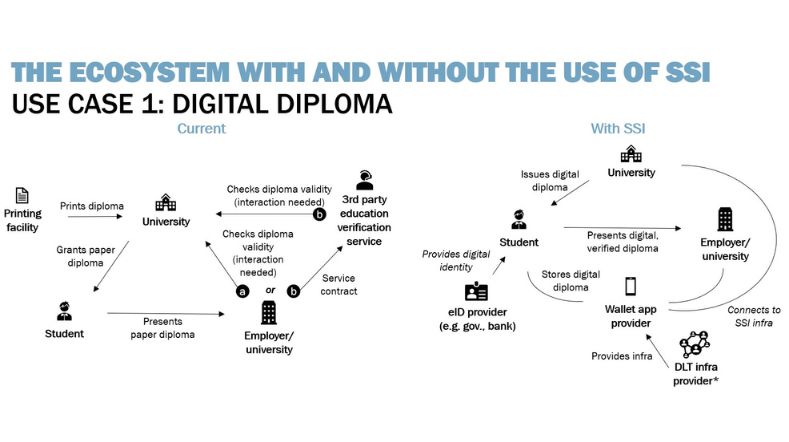
SSI (Self-sovereign identity) is a set of cybersecurity technologies that support the exchange and processing of personal information (passport, diploma, driver’s license, bank, insurance, chamber-of-commerce, ...) in a privacy-by-design manner.
It enables counterparties to obtain sufficient assurances to enter a transaction, whether it is a car rental, a webshop purchase, a mortgage, a new employment, or other.
For example, by sharing a diploma via SSI, the prospect employer can automatically verify the authenticity of the diploma and the graduate, without needing to inform and check with their university.
Latest in-depth articles
Read our latest articles for professionals to see what SSI technology we have developed and how we use SSI in our projects.
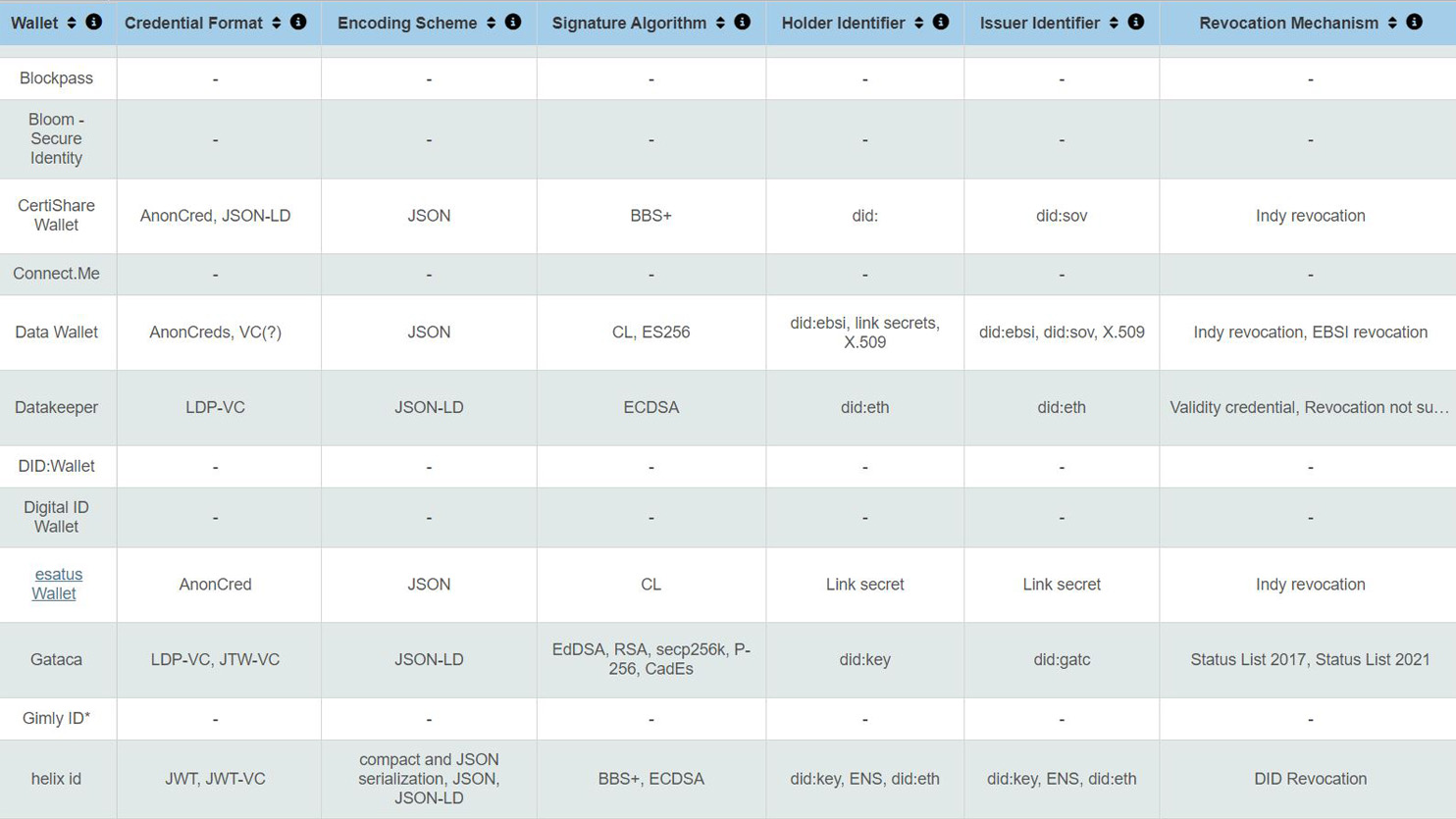
Digital identity wallets: a technical overview
The digital wallet overview, introduced in this blog, helps businesses, developers and end-users to decide which wallet to use for their business case.
The business side of SSI – what type of business model should I choose?
The technical maturity of SSI (Self-Sovereign Identity) is high enough to not be the main barrier anymore for adoption, but it's not enough to achieve large-scale usage. The business aspects around introducing digital credentials for SSI need to be clarified.
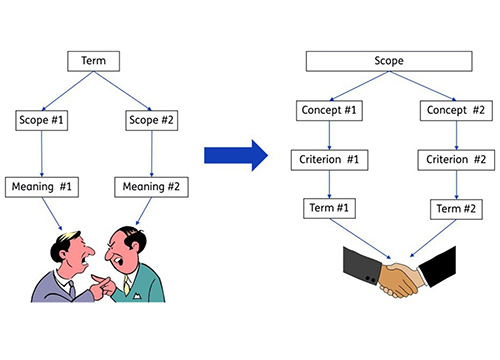
Effectively resolving semantic discussions for data sharing
The TNO Terminology Design methodology can help to find a effectively resolve in semantic discussions when developing interoperable solutions for data sharing.
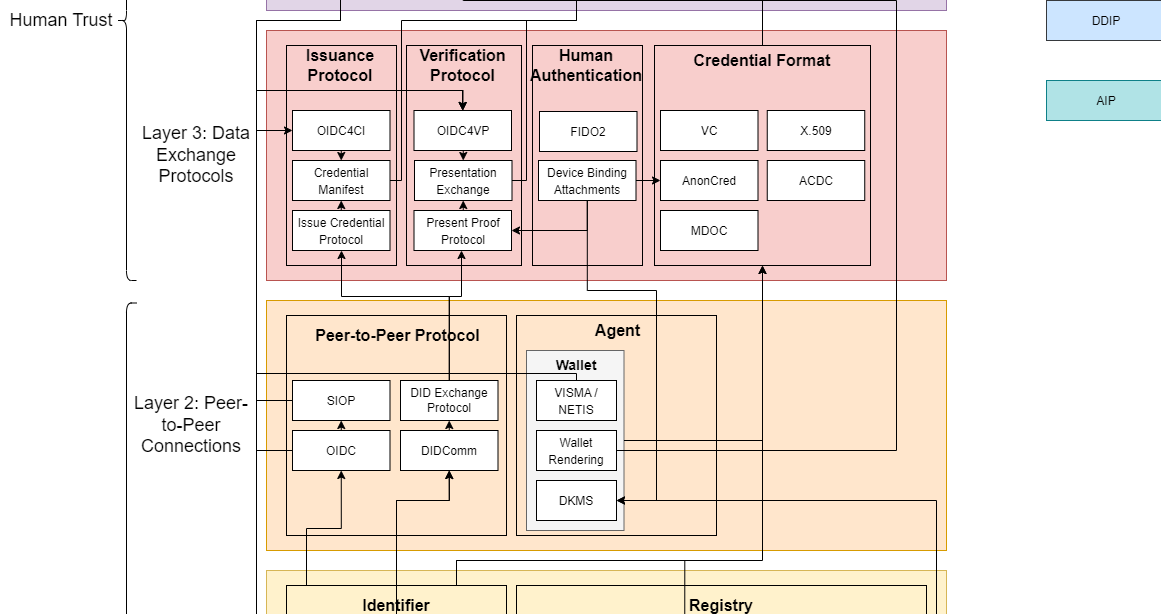
What are those SSI standards?
It can be difficult for SSI adopters to figure out which standards in the context of SSI are relevant and how they relate to other standards. Our standardisation overview helps with this, by giving insight in the positioning of standards in the context of SSI.

Solving the effort of offering support for a great variety of wallets
Due to competing technological approaches, there is fragmentation within the SSI ecosystem. Read our solution to this problem: TNO EASSI.

FEDeRATED: project for digital co-operation in logistics
Find out more about FEDeRATED: an EU CEF project for digital cooperation in logistics comprising 15 partners in 6 EU member states
Self Sovereign Identity, a Paradigm Shift for organisations
How ready is the private sector to adopt digital trust? Reaping the benefits of Self Sovereign Identity requires a fundamental paradigm shift for your organisation.
Protecting Sensitive Parts of Credentials with Cryptographically Enforceable Policies
The Self-Sovereign Identity paradigm gives users control over their own data. This control does not mean that they should always be able to see that data.
The Myth Of Control in Self-Sovereign Identity
The term `Self-Sovereign Identity` (SSI) starts from the principle "Users should control their identity". Read how we distinguish reality from wishful thinking.
More articles
-
SSI and Guardianship - A New Credential Type (blog 1/3)
-
SSI and Guardianship - What's Next? The Assurance Community (blog 3/3)
-
Self-Sovereign Assets: Roads and roadblocks towards supporting digital assets in an SSI context
- Self-Sovereign Communication: emerging technologies for up to self-sovereign communication
- Verify the Verifiery: anti-coercion by design
- Self-sovereign identity: the good, the bad and the ugly
Get inspired
Assuring Digital Identity


Rules as Code


Digital Product Passport


Data spaces in healthcare


GPT-NL boosts Dutch AI autonomy, knowledge, and technology





